
A Risk-Based Approach to Financial Crime Mitigation – Part 1
Managing Risk – Laying the Foundations
What is Financial Crime Mitigation (FCM)
Managing risk is the supreme discipline in banking and one which is widening everyday. Most financial institutions (FIs) are accustomed to manage risks in areas like credit risk or market risk where the hazards can be calculated and quantified and where they are assessed prior to accepting them.
However, financial crime risks differ from the “normal” risk assessment, as they are a “consequential” risk, this means that financial crime risks with some customers may only become evident once the customer is already transacting through the account. This is the reason why monitoring of customer transactions is a fundamental component of the Risk-Based Approach (RBA).
Financial crime risks reflect an FIs external and internal environment including mitigating controls.
As criminals seek to launder proceeds gained from financial crime through the financial system, the focus on the RBA is on money laundering (ML) risks. FATF, EU anti-money laundering directives, US BSA/AML and many other national legislations put the RBA at the centre of Anti-Money-Laundering (AML) and combating the financing of terrorism (CFT) regimes.
Best practice in FCM – Risk Management Process
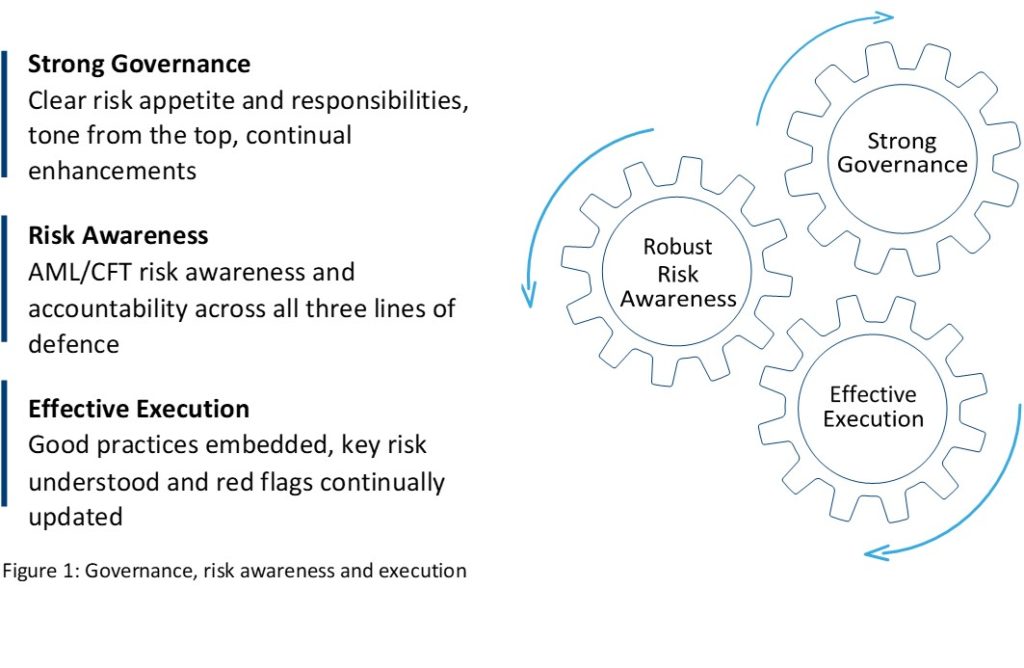
A robust corporate risk awareness programme which is rigorously policed ensures allocation of clear responsibilities and drives continual enhancements.
The risk assessment forms the basis for an FI’s RBA and reviews robustness of all three lines of defence, embedded good practices, and whether updates to the identified key risks and their red flags are understood.
The Risk Management Process as described in the standard ISO 31000:2018 is an integral part of a company’s Risk Management Framework, which follows the PDCA cycle (Plan – Do – Check – Act) from W. Edward Deming.
The FCM Cookbook explains, the structure of this standard aims to integrate and include actual and future internal and external changes into management decisions in order to optimize and improve strategic and operational process goals. The PDCA cycle is a proven and well-established problem solving principle. “Do” of the PDCA cycle invokes the risk management process. Once the context is set, i.e. the scope defined, the risk assessment runs through the steps to identify, analyse and evaluate risks. Management of risks includes the decision to treat, tolerate, transfer or terminate a risk.
This approach to risk management (and risk assessment to set the basis for RBA) is widely used in the financial industry and other industries.
History of Risk-Based Approach
When legislation regarding KYC (Know-Your-Customer) and Anti-Money Laundering (AML) came into force in many countries in the 90s, there was a mainly a check-box approach to risk assessments, applicable to all banking business models. This had the effect that banks missed real risks, to which they were exposed since they approached the process of identifying risk in a mechanical way.
This approach was doomed to fail as the risks in retail banking are substantially different compared to the ones in institutional banking. Hence, banks with their compliance efforts frequently failed to meet regulatory expectations.
Risk Assessment
The FATF revision in 2010 brought much clearer definitions of RBA and the concept of “effective risk-based controls”, which made national legislators responsible for defining what is deemed to be effective. Since then, many regulators now use the term “effectiveness” in their guidance and discussions with the FIs. The FATF revision of the 40 Recommendations in 2012 requires countries to assess and understand their ML- and TF- threat risks.
National regulations require FIs to demonstrate strong governance and a robust risk awareness within their organisations, backed and supported with an effective execution. The risk appetite is a key influence upon a firm’s strategic goals and drivers, which amount and type of risks the firm is willing and able to accept and which measures are needed to control these risks. The FCM Cookbook gives more detail about the processes, which are involved in achieving this compliance, and much more detail into how these procedures should be executed.