
Data Sovereignty in a Borderless World
By Sonal Rattan, CTO and Co-founder, eXate
As organisations scale globally and accelerate cloud adoption, data is no longer confined by geography, but regulation still is. This mismatch is creating one of the most pressing challenges in modern enterprise strategy: how to maintain control over data that is constantly in motion across jurisdictions.
Data sovereignty has emerged as the critical battleground.
It is no longer just a compliance checkbox. It is a question of trust, control, and ultimately, competitive advantage.
The Growing Complexity of Data Sovereignty
The regulatory landscape has changed dramatically in recent years. With over 130 countries now enforcing data protection laws, organisations must navigate a patchwork of requirements governing how data is collected, stored, processed, and transferred.
At the same time, geopolitical tensions and extraterritorial legislation have added another layer of complexity. Laws that allow authorities to request access to data stored abroad have raised concerns about loss of control, conflicts between legal regimes, and the exposure of sensitive information.
For global enterprises, this creates a fundamental tension:
- Data must flow freely to support global operations
- However, it must also remain governed by local laws
Traditional approaches to managing this tension are no longer sufficient.
Beyond Location: What Data Sovereignty Really Means
Data sovereignty is often misunderstood as simply “where data is stored.” In reality, it is about which laws apply to that data and who ultimately controls it.
To understand this properly, it helps to distinguish between three commonly conflated concepts, Data Residency, Localisation and Sovereignty.
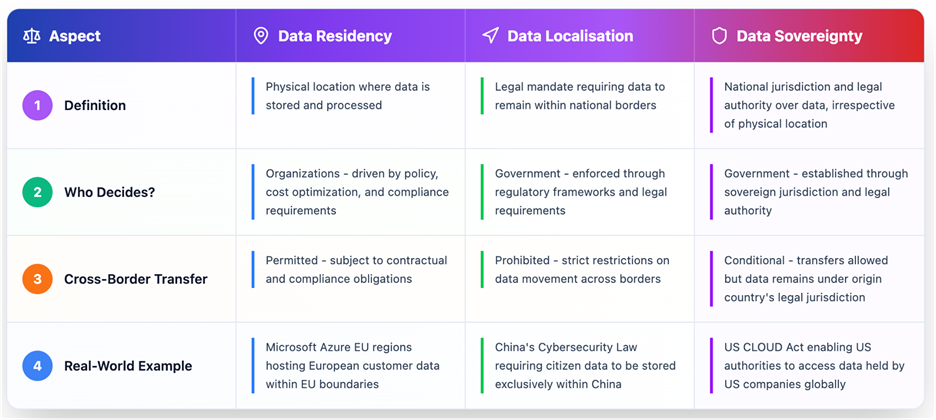
This distinction is critical. An organisation may store data in one country, process it in another, and still be subject to regulations from a third.
In this environment, sovereignty cannot be guaranteed by infrastructure decisions alone.
Why Encryption Alone Isn’t Enough
For years, encryption has been treated as the primary solution to data protection. While it remains essential, it does not fully address the challenges of data sovereignty.
There are several reasons for this:
- Encrypted data is still regulated. Even when protected, data may still be considered personal or sensitive under law.
- Key management introduces new risks. If encryption keys are not fully controlled by the organisation, sovereignty can be compromised.
- Future threats are emerging. Advances in quantum computing raise concerns about the long-term resilience of current encryption methods.
Encryption reduces risk, but it does not guarantee control.
The Shift to Data-Centric Sovereignty
To truly address data sovereignty, organisations are moving toward a more sophisticated model: data-centric protection.
This approach recognises that control cannot be guaranteed by location alone. In highly distributed, cloud-based environments, data is constantly in motion across systems, regions, and users. As a result, sovereignty must travel with the data itself. Instead of relying solely on where data is stored, organisations are embedding governance, security, and compliance directly into the data layer.
At the heart of this shift is a move toward policy-driven control. Rather than applying broad, static rules at the infrastructure level, organisations are defining granular policies that determine how data can be accessed, processed, and shared based on context. This includes factors such as jurisdiction, user identity, and intended purpose. These policies are then enforced consistently, regardless of where the data resides or how it moves.
This model is underpinned by continuous visibility. Sensitive data is no longer treated as a static asset but as something that must be dynamically identified and classified across the entire data estate. Real-time discovery and classification allow organisations to understand exactly what data they hold, where it exists, and how it should be protected, enabling more precise and consistent enforcement of sovereignty requirements.
Alongside this, organisations are increasingly adopting privacy-enhancing techniques such as tokenisation and pseudonymisation. These techniques allow sensitive data to be protected at a granular level while still enabling it to be used for analytics, operations, and innovation. By separating sensitive attributes from usable data, businesses can maintain functionality without exposing regulated information.
Finally, this approach enables a more intelligent model of data movement. Instead of restricting all data flows, organisations can distinguish between sensitive and non-sensitive data. Sensitive data can remain protected or localised as required, while non-sensitive data is allowed to move freely across borders. This creates a balance between compliance and operational efficiency, allowing global systems to function without violating local regulations.
Taken together, this represents a fundamental shift in how sovereignty is enforced. The focus moves away from controlling where data lives and toward controlling how data behaves.
Where eXate Fits
eXate addresses data sovereignty at its source, the data layer itself.
Through a combination of centralised policy management, automated data discovery and classification, and advanced privacy-enhancing techniques, eXate enables organisations to enforce sovereignty requirements in real time across data in motion, at rest, and in use.
By protecting sensitive data at a granular level and separating it from non-sensitive data, eXate allows organisations to meet data residency, localisation, and sovereignty requirements without limiting global operations. Its approach ensures that data remains secure, compliant, and under the organisation’s control, regardless of where it travels.
In a world where data is constantly crossing borders, true sovereignty comes not from restricting movement, but from maintaining control at every point along the way.
Sovereignty, by design.
If your organisation is struggling to maintain true data sovereignty as information moves through global operations, testing environments, or large‑scale migration programmes, now is the time to take control at the data layer itself. eXate enables you to enforce consistent, policy‑driven protection wherever your data travels – without slowing innovation or limiting how your teams work. If you want to reduce compliance risk, regain visibility, and ensure sovereignty that moves with your data, book a Sovereign Data Control Consultation and see how eXate can transform your end‑to‑end data strategy.